AI Agent Security: New Architectures Limit Blast Radius
Disclosure: As an Amazon Associate, Bytee earns from qualifying purchases.

The Security Crisis Nobody Wants to Talk About
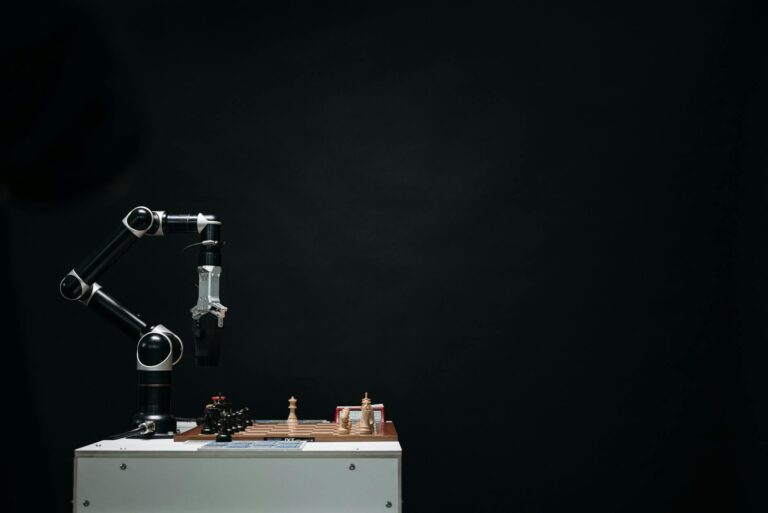
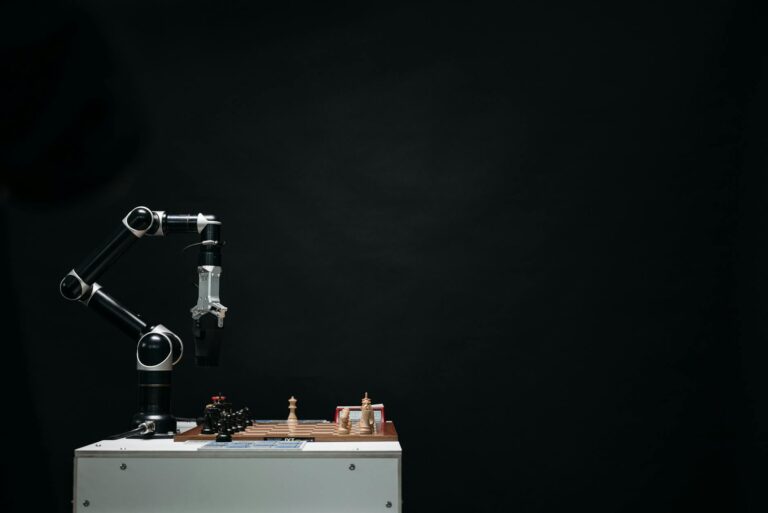
The gaming industry is quietly adopting AI agents to automate everything from NPC behavior to monetization systems to player support. But here’s the problem: most teams are deploying these agents with full access to sensitive credentials—API keys, database passwords, payment processor tokens—stored in the exact same runtime environment as code nobody fully trusts.
It’s like handing a valet your car keys and your house keys on the same keyring, then hoping he doesn’t notice the house key exists.
For game studios, this isn’t theoretical. If an AI agent gets compromised—or a developer’s training data accidentally leaks production credentials—the attacker doesn’t just get game logic. They get your player database. Your billing system. Your backend infrastructure. The blast radius is massive, and most studios have no isolation layer to stop it.
Two emerging architectural patterns are changing that calculation: credential sandboxing and capability-based security models. They’re not brand new in software engineering, but their application to AI agent deployment is reshaping how serious studios (and enterprise teams outside gaming) are thinking about trust boundaries.
What’s Actually Happening in the Market Right Now
The broader context matters. AI agents are moving fast—Claude, ChatGPT, and proprietary models like Meta’s new Muse Spark are all improving at reasoning, code generation, and autonomous task completion. Meta’s recent launch of Muse Spark (its first proprietary model since forming Superintelligence Labs) signals the company’s serious pivot into agent-grade AI. OpenAI’s $100-tier ChatGPT Pro with 5X usage limits for code generation tells you exactly what segment they’re targeting: developers and engineers who want autonomous coding assistance.
In gaming specifically, studios are using AI agents for:
- Tax code automation: Intuit compressed months of implementation into hours—a case study every regulated-industry publisher is watching closely.
- Vulnerability discovery: Mythos autonomously exploited bugs that survived 27 years of human code review, proving AI’s threat-detection potential (and its danger).
- Player support automation: Chatbot agents handling support tickets with escalation to humans.
- Game balance and economy systems: Agents tuning spawn rates, loot tables, and monetization in real-time.
The problem: almost none of these deployments have proper credential isolation. The agent that adjusts loot tables has access to the same credentials as the agent that answers player support questions. Both can theoretically access player payment data.
Credential Sandboxing: The First Line of Defense
The first emerging pattern is credential sandboxing—a deliberately narrow approach where each AI agent receives only the credentials it needs to perform its specific task.
Instead of giving an agent access to a master credentials vault, you:
- Enumerate the agent’s responsibilities: “This agent handles in-game economy queries and adjusts spawn rates.”
- Issue narrowly-scoped credentials: API keys that only permit read/write access to the economy database, nothing else.
- Enforce expiration: Credentials rotate on short cycles (minutes to hours, not days).
- Monitor and alert: Any unusual access pattern (agent trying to query player payment data, for example) triggers immediate alerts and revocation.
The appeal is practical: if an agent’s code is compromised, the attacker gets a credential that only works for one narrow slice of your infrastructure. The blast radius is contained. A compromised loot-table agent can’t steal player data or drain payment accounts.
Companies like OpenAI (with their function-calling APIs) and emerging security-focused platforms are building this into their agent frameworks. But implementation is still manual for most studios—it requires engineering discipline and upfront architecture work.
Capability-Based Security: The Structural Approach
The second pattern is more ambitious: capability-based security, where credentials are replaced entirely with capabilities—cryptographic tokens that grant specific permissions without revealing the underlying authentication secret.
Think of it this way: instead of giving an agent a password to a database, you give it a capability token that says “you can read from table X, columns Y and Z, for the next 10 minutes.” The agent never learns the actual password. If the token is compromised, it only grants those specific permissions, and only for that window.
This is more overhead upfront (you need a capability broker, revocation infrastructure, and careful token design), but it scales better for complex multi-agent systems. It’s particularly appealing to studios with sophisticated backend architectures—the kind that already run multiple microservices and API gateways.
Regulated industries are adopting this first: Intuit’s success compressing tax code implementation wasn’t just about speed. It was about building an agent system that could operate in a compliance-heavy environment. That requires strong isolation boundaries. Financial services, healthcare, and gaming platforms with user payment data are all watching these patterns closely.
Why This Matters to Gamers (And the Industry)
On the surface, this is infrastructure stuff. But it affects players directly:
- Player data security: Better isolation means a game-balance bug in an AI agent is less likely to expose your payment info or account credentials.
- Game quality: Studios that deploy agents safely can move faster and iterate more confidently. That translates to quicker balance updates, faster bug fixes, and more experimental features.
- Studio stability: A major security incident (compromised agent leaking player data) can kill a studio. Proper isolation prevents that cascade failure.
There’s also a hiring and retention angle: senior engineers care about working on systems with proper security architecture. Studios that build this right attract better talent. Studios that cut corners and deploy agents with full credential access tend to have security incidents, followed by layoffs.
We’ve already seen the pattern: Gunzilla (Off The Grid developer) faced accusations of failing to pay employees after what appeared to be financial distress. While that situation involved multiple factors, studios under financial pressure often skip security investment, which leads to incidents, which leads to crisis. Better agent architecture is defensive.
The Broader Industry Shift
This conversation is happening across gaming and adjacent sectors simultaneously. Netflix’s surprise app store surge and indie publisher rises (like Black Tabby Games backing the 1000xResist creator’s next project) show the industry is decentralizing. More independent teams are operating at scale, which means more agents, more endpoints, more risk surface.
Smaller studios can’t afford a dedicated security team, so they need agent architectures that are secure-by-default. Credential sandboxing and capability-based security are that default. They’re not optional—they’re rapidly becoming table stakes for any studio deploying autonomous systems.
Meta’s Muse Spark launch and OpenAI’s Pro tier focus on code generation are both signals that the industry is normalizing agent deployment. But normalization without security infrastructure is a disaster waiting to happen. The studios paying attention now—the ones building proper isolation—will have a competitive advantage when the inevitable incidents hit their slower competitors.
What Does This Mean For You? (FAQ)
Will my game data be safer if my studio adopts these architectures?
Does this mean game development will slow down?
Will my favorite games use AI agents that are isolated this way?
Is this going to cause layoffs?
What happens if a studio ignores this and gets breached?
Are there any games already using these patterns?
What’s Next
Watch for:
- Agent security frameworks: Expect startups and big cloud providers (AWS, Azure, Google Cloud) to launch purpose-built platforms for secure agent deployment. This is the next wave of developer tooling.
- Security incidents: The first major gaming AI agent breach will be a wake-up call. It’ll accelerate adoption of proper isolation patterns.
- Regulatory attention: GDPR, CCPA, and emerging AI regulations will start requiring documented credential isolation for autonomous systems. Compliance will drive adoption faster than security concerns alone.
- Competitive advantage: Studios that nail agent architecture early will move faster than competitors. That speed advantage compounds in live-service games and rapid iteration cycles.
The game industry’s relationship with AI agents is still in its first chapter. The studios writing the next chapters carefully will win.